C5:2026 – The New Standard for Cloud Security is Here
The German Federal Office for Information Security (BSI) has officially released the final version of the Cloud Computing Compliance Criteria Catalogue (C5:2026). Replacing the 2020 version, this final publication cements C5 as the premier benchmark for cloud security and digital sovereignty in the European market.
While the previous version (C5:2020) was already a global standard, C5:2026 is a substantive revision designed to address modern technological shifts like Confidential Computing, Post-Quantum Cryptography, and the regulatory requirements of the NIS2 Directive.
Here is a detailed look at the finalized C5:2026 catalogue, how it functions, and what has changed in the final release.
What is C5?
C5 stands for Cloud Computing Compliance Criteria Catalogue. It is a government-backed standard that defines a baseline level of information security for cloud service providers (CSPs).
C5 is not a simple “pass/fail” certification. Instead, it is a reporting standard where an independent auditor evaluates a CSP against a structured catalog of criteria. The output is a detailed attestation report. This provides customers with high-level transparency into a provider’s security posture, enabling technically sound risk assessments and sovereign decisions.
How the Framework Works
The C5 framework dictates what must be audited, while relying on international standards for how the audit is conducted.
C5 audits must be conducted according to the ISAE 3000 (Revised) standard (or national equivalents like IDW PS 860). These audits provide “reasonable assurance” rather than “limited assurance”.
Providers generally issue two types of reports:
Type 1: Confirms the suitability of the control design at a specific point in time.
Type 2: Confirms both the suitability of design and the operating effectiveness of controls over a period (typically 3 to 12 months).
The C5:2026 Criteria
The C5:2026 catalogue is engineered for high-level transparency and rigorous auditability. It is structured in a hierarchical manner that bridges high-level security objectives with specific, granular technical controls.
1. Information on the General Conditions (GC)
Before addressing specific security criteria, the framework requires providers to disclose six General Conditions (GC). These conditions are not technically “audited” for security effectiveness in the same way as technical controls, but they must be documented and verified to provide customers with the context necessary for technically sound risk assessments.
GC-01: Law and Geography: Details on applicable law, jurisdiction, and the exact locations (partitions, regions, and zones) where customer, account, and derived data are processed.
GC-02: Regular Operations: Binding information on service availability, incident prioritization, and recovery times.
GC-03: Emergency Parameters: Critical recovery data including RTO, RPO, and Maximum Tolerable Period of Downtime (MTPD).
GC-04: Availability Approach: Architectural design principles ensuring infrastructure and service resilience.
GC-05: Government Investigation Requests: Transparency on how legal requests are verified, how customers are notified, and technical decryption capabilities.
GC-06: Certifications and ESG: Disclosure of valid certificates (e.g., ISO/IEC 27001, GDPR) and adherence to Environmental, Social, and Governance (ESG) standards like the CSRD.
2. The 17 Security Domains
The heart of the catalogue consists of 17 thematic domains aligned with the 2013 revision of ISO/IEC 27001. These domains cover the entire spectrum of cloud security, from organizational management (OIS) and human resources (HR) to highly technical areas like Cryptography (CRY) and Container Management (OPS).
A major innovation in C5:2026 is the refined structural depth designed to align with the European Cloud Certification Scheme (EUCS):
Criteria: Each domain contains several criteria that define a specific security requirement.
Sub-Criteria: To ensure precise auditing, criteria are now broken down into distinct sub-criteria. This allows Cloud Service Providers (CSPs) to map their specific internal controls directly to clear, delineated requirements, removing the ambiguity of whether a broad “criterion” has been fully met.
4. Basic vs. Additional Criteria
To accommodate varying levels of data sensitivity, the requirements are tiered:
Basic Criteria: These represent the mandatory minimum security baseline for a cloud service. Every CSP must meet 100% of the basic criteria to claim C5 compliance.
Additional Criteria: These provide a starting point for customers with higher protection needs (e.g., government or critical infrastructure). In the 2026 version, these are explicitly classified by their relationship to the basics:
Additional Sharpen (AS): These “sharpen” an existing basic criterion with stricter requirements (e.g., increasing the frequency of a security task) and act as a replacement for the basic version in the audit report.
Additional Complement (AC): These introduce entirely new security aspects or technologies not addressed by the basic criteria (such as Post-Quantum Cryptography).
This modular structure allows a C5 report to be tailored: while the “Basic” tier ensures a common industry standard, the “Sharpened” and “Complementary” tiers allow providers to demonstrate the specialized resilience required for digital sovereignty
C5 vs. SOC 2: What Are the Differences?
While both provide security assurance, they differ in philosophy:
Principles vs. Prescriptive Criteria: SOC 2 is principles-based; the provider defines their own controls. C5 is criteria-based and prescriptive; the BSI defines exactly which criteria must be met.
Reporting Depth: C5 requires the disclosure of General Conditions (like data residency and jurisdiction), which provides a higher level of transparency regarding digital sovereignty than a standard SOC 2 report.
Combined Audits: CSPs can perform “audit once, report twice” by mapping internal controls to both SOC 2 and C5, significantly reducing audit fatigue.
What Has Changed in the Final C5:2026 Version?
The final publication represents a significant modernization to align with the European Cloud Certification Scheme (EUCS).
Structural Revision: Criteria are now broken down into sub-criteria. This allows for more precise mapping to a CSP’s internal controls and greater clarity for auditors.
Modern Technical Focal Points:
Containers: Dedicated domain for container management and lifecycle security.
Confidential Computing: Requirements for protecting data “in use” via Trusted Execution Environments (TEEs).
Post-Quantum Cryptography (PQC): CSPs must now document a PQC strategy to address future quantum computing threats.
Enhanced Supply Chain (SSO): Increased focus on Supply Chain Management, requiring CSPs to provide more transparency regarding subcontractors and data flows throughout the service chain.
Sovereignty Sharpening: Clearer definitions of data types ensure that criteria apply correctly to customer-owned data versus telemetry/log data (derived data).
Transition and Applicability
The BSI has established a clear timeline for the new standard. C5:2026 criteria shall be applied in audit engagements with specified dates or periods beginning on or after June 1st, 2027. Earlier adoption is permitted and encouraged for providers looking to demonstrate “state of the art” compliance early.
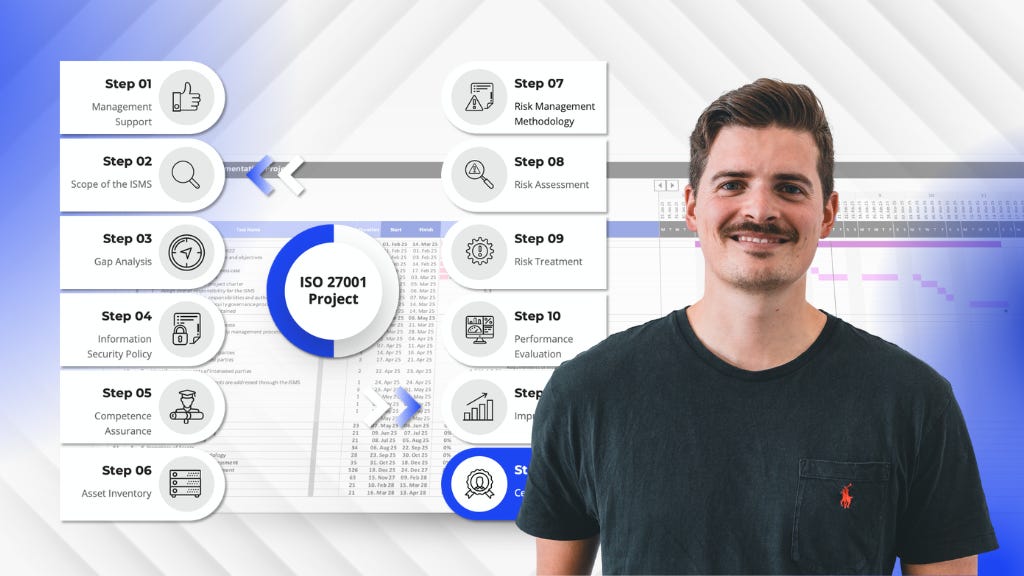
From ZERO to AUDIT-READY in 12 Steps
If you are responsible for an ISO 27001 implementation project, you are fighting a battle against the clock.
The standard tells you WHAT must be done,
but it leaves the HOW entirely to your imagination.
This leaves you staring at a blank map, forced to build an ISMS from scratch while the deadline approaches.
Our ISO 27001 Lead Implementer Framework gives you the Roadmap, Project Plan, Templates and Training to be audit-ready in months, not years.