Implementing ISO 27001 can often seem daunting due to its abstract nature and the lack of detailed implementation instructions. However, a structured 10-step approach can make this process manageable for any organization, regardless of its size or industry. Here's a breakdown of these steps to effectively implement an Information Security Management System (ISMS) in accordance with ISO 27001.
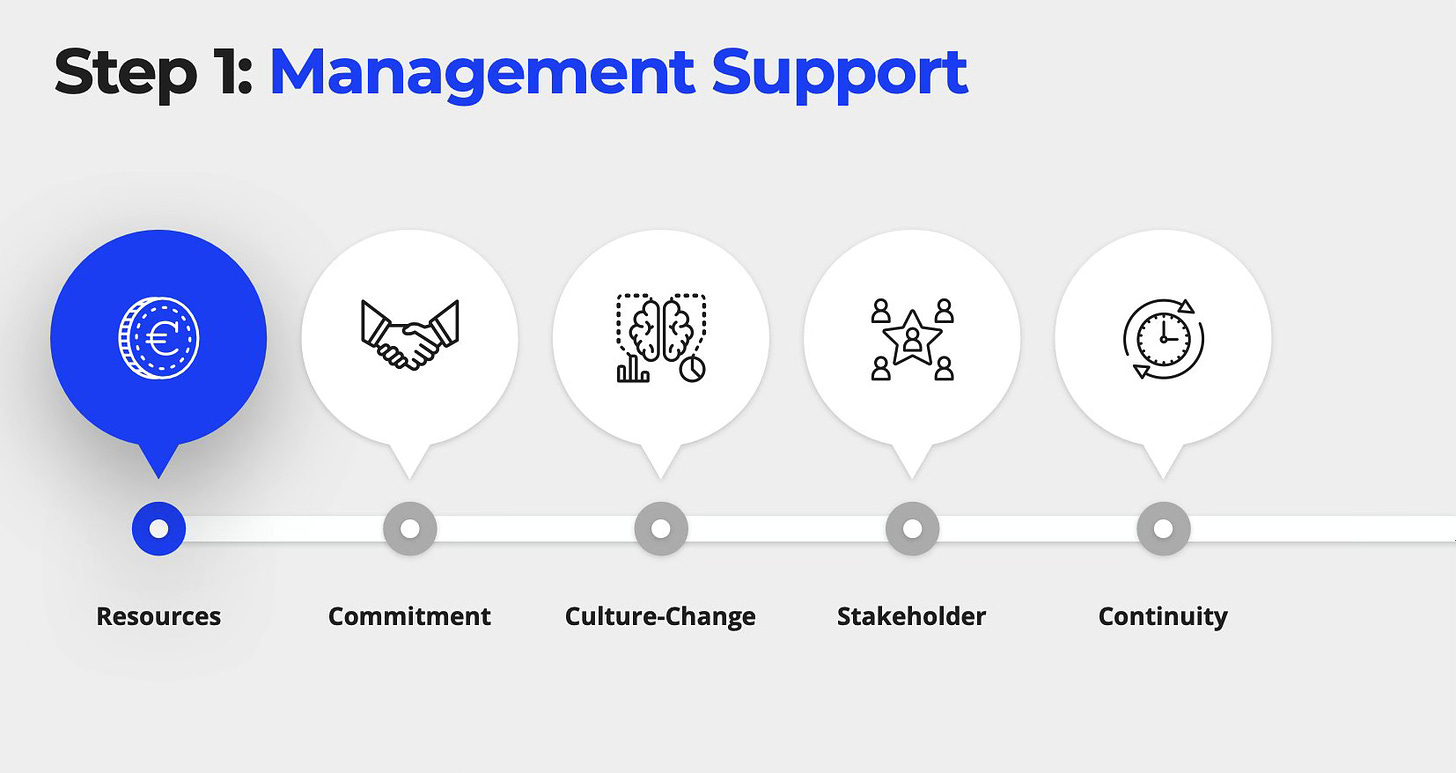
Step 1: Obtain Management Support
The journey begins with obtaining support from top management. Their approval is critical as implementing an ISMS demands significant resources. Without this backing, progressing further is inadvisable.
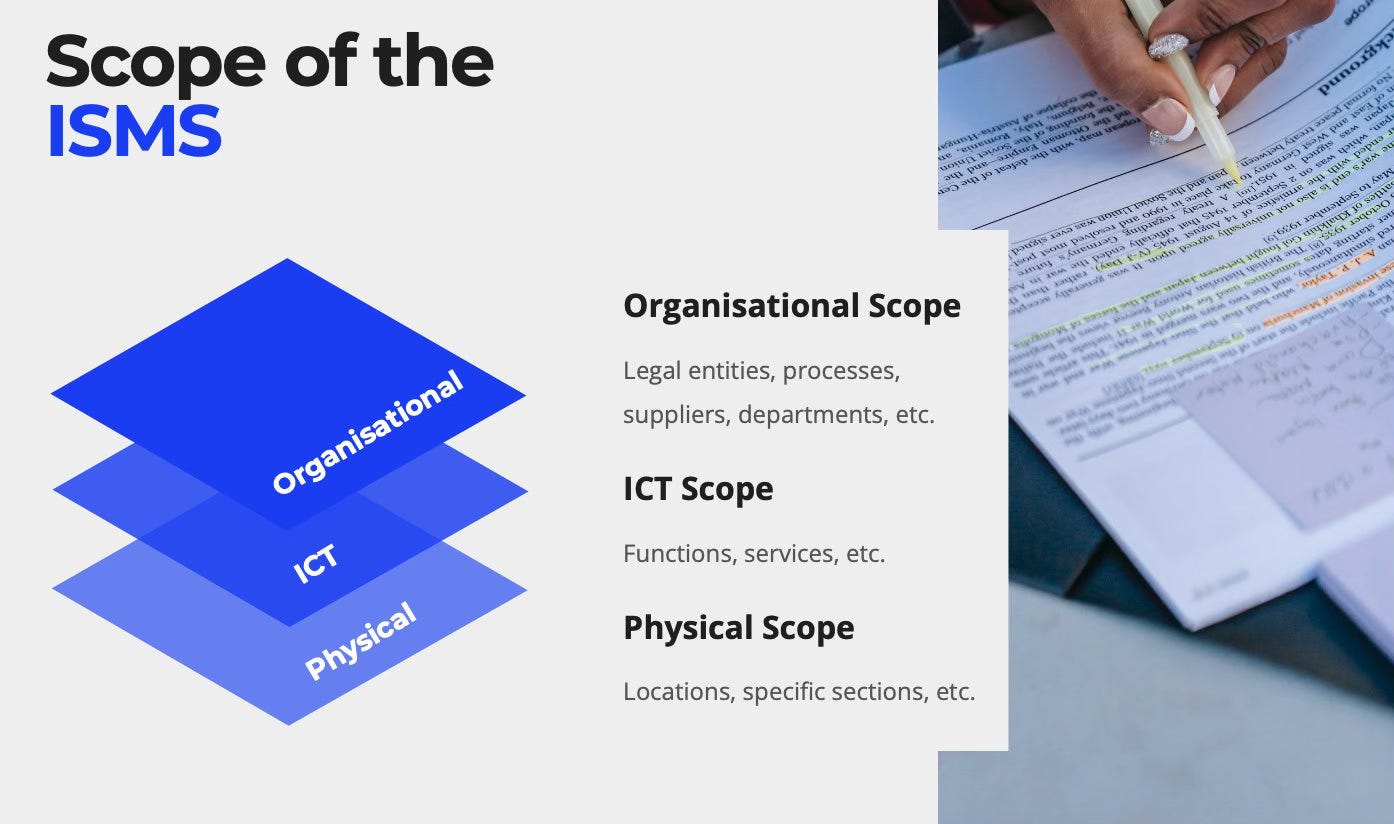
Step 2: Determining the ISMS Scope
Deciding the scope of the ISMS is a strategic early step. It involves selecting specific parts, processes, or services of the organization that will fall under the ISMS.
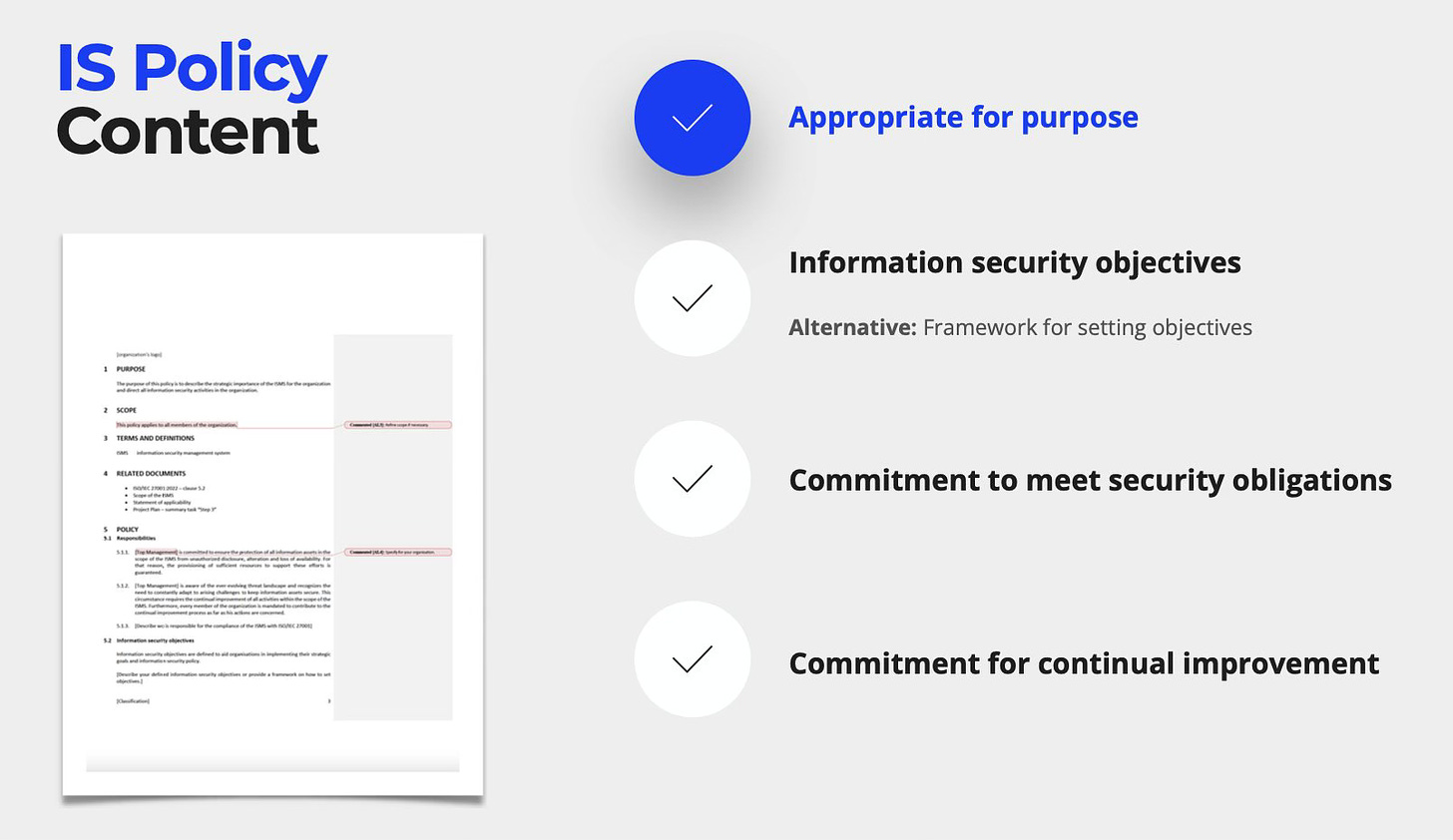
Step 3: Establishing Information Security Policy
This step involves writing a high-level policy that outlines the organization's information security objectives, laying the groundwork for the ISMS.
Step 4: Asset Identification and Classification
Identify and classify assets within the ISMS scope. A thorough asset inventory is crucial to understand what requires protection.
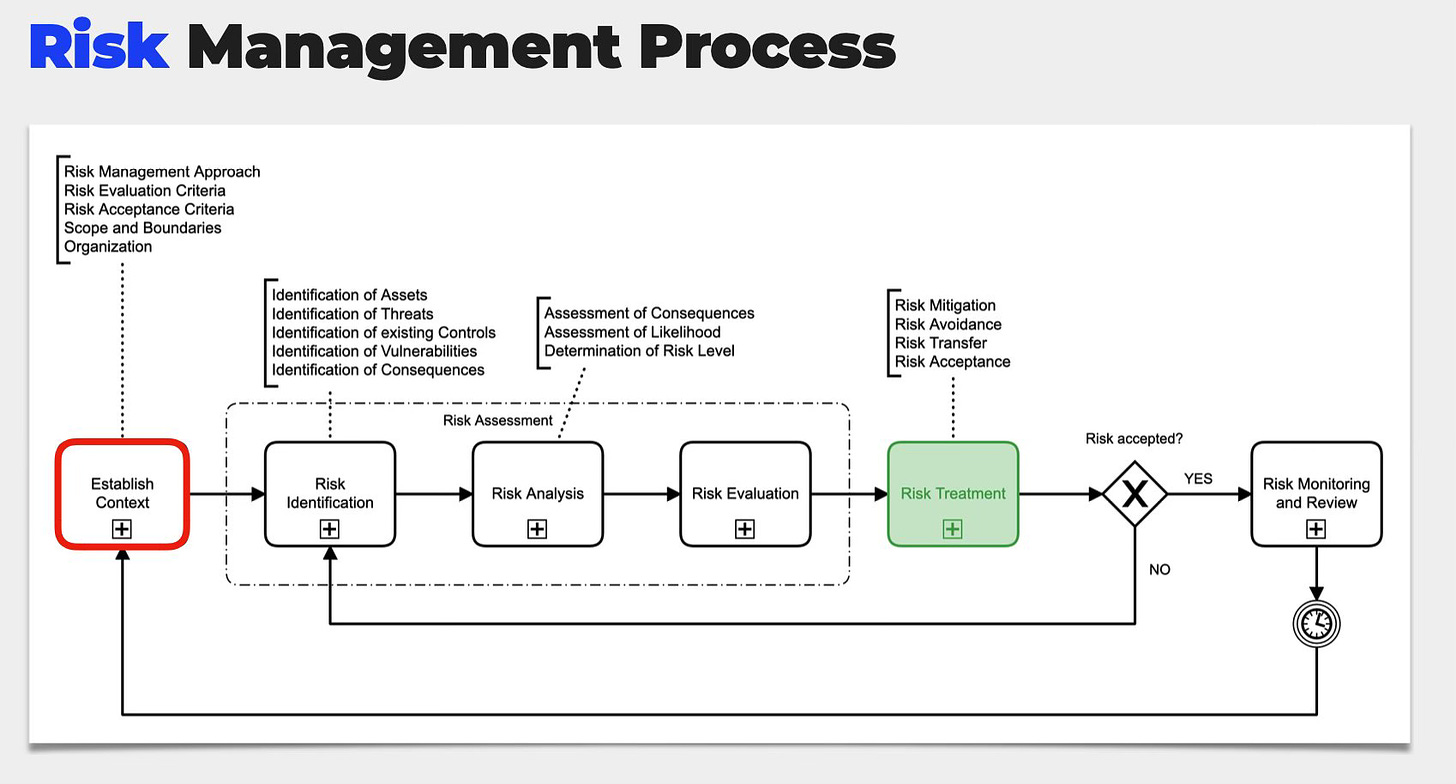
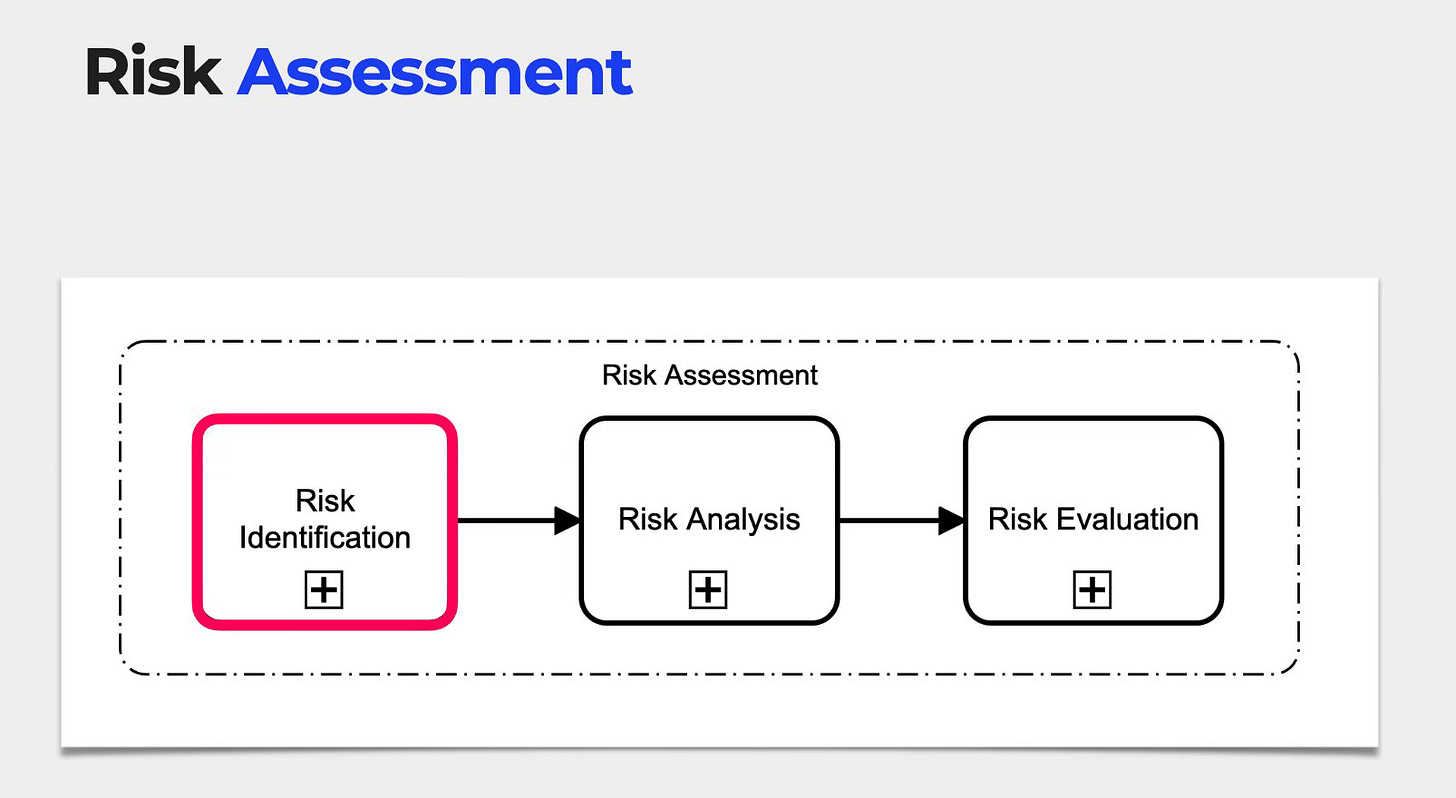
Step 5: Risk Management Methodology
Develop a process and methodology for conducting information security risk assessments and treatments, including defining the organization’s risk appetite and key criteria.
Step 6: Information Security Risk Assessment
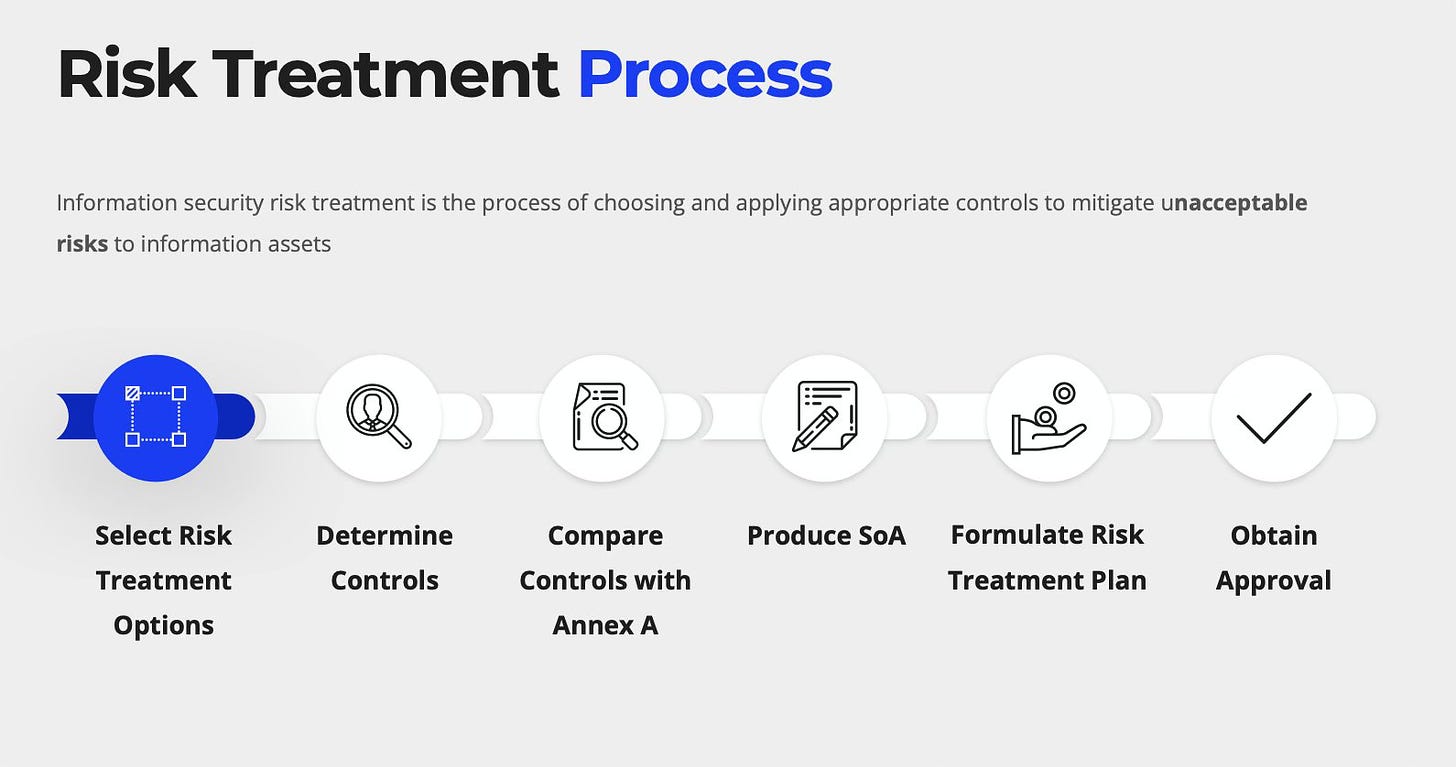
Step 7: Information Security Risk Treatment
These steps, being the most extensive, involve conducting risk assessments and selecting risk treatment options based on the established methodology.
Step 8: Performance Evaluation
Evaluate the ISMS performance by monitoring key performance indicators (KPIs), conducting internal audits, and providing top management with relevant data for management review.
Step 9: Improvement
Based on the performance evaluation, implement necessary corrections and corrective actions to improve the ISMS and ensure compliance with ISO 27001 standards.
Step 10: Certification Audit
Once these steps are effectively executed, the organization is ready to seek ISO 27001 certification.
By following this structured approach, organizations can navigate the complexities of ISO 27001 implementation, ensuring a robust and compliant ISMS tailored to their unique needs and circumstances.
Whenever you're ready, there are 2 ways I can help you:
ISO 27001 Lead Implementer Course: Join 6,500 students in mastering ISO/IEC 27001:2022. This comprehensive 7 hour course will teach you a proven 10-Step methodology with ready-to-use templates, saving you and your organisation hundreds of hours.
ISO 27001 Project Plan: Simplify Your Path to Compliance with a customizable Project Plan and supporting Resources.
Refer Friends, Earn Rewards!
You’re just 1 referral away from the first of many free resources.













Implementing ISO 27001: A generic 10-Step Approach